Braindump2go Updates Cisco 300-206 VCE Exam Questions for Free Download (111-120)
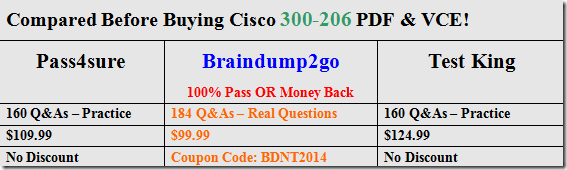
Cisco Official News: Instant Download 300-206 PDF Files! New Updated 184 Exam Questions and Answers help 100% Exam Pass! 300-206 Certification Get Quickly!
Vendor: Cisco
Exam Code: 300-206
Exam Name: Implementing Cisco Edge Network Security Solutions
Keywords: 300-206 Exam Dumps,300-206 Practice Tests,300-206 Practice Exams,300-206 Exam Questions,300-206 PDF,300-206 VCE Free,300-206 Book,300-206 E-Book,300-206 Study Guide,300-206 Braindump,300-206 Prep Guide
QUESTION 111
Which ASA feature is used to keep track of suspected attackers who create connections to too many hosts or ports?
A. complex threat detection
B. scanning threat detection
C. basic threat detection
D. advanced threat detection
Answer: B
QUESTION 112
What is the default behavior of an access list on a Cisco ASA?
A. It will permit or deny traffic based on the access list criteria.
B. It will permit or deny all traffic on a specified interface.
C. It will have no affect until applied to an interface, tunnel-group or other traffic flow.
D. It will allow all traffic.
Answer: C
QUESTION 113
When configuring a new context on a Cisco ASA device, which command creates a domain for the context?
A. domain config name
B. domain-name
C. changeto/domain name change
D. domain context 2
Answer: B
QUESTION 114
Which statement describes the correct steps to enable Botnet Traffic Filtering on a Cisco ASA version 9.0 transparent-mode firewall with an active Botnet Traffic Filtering license?
A. Enable DNS snooping, traffic classification, and actions.
B. Botnet Traffic Filtering is not supported in transparent mode.
C. Enable the use of the dynamic database, enable DNS snooping, traffic classification, and actions.
D. Enable the use of dynamic database, enable traffic classification and actions.
Answer: C
QUESTION 115
Which Cisco switch technology prevents traffic on a LAN from being disrupted by a broadcast, multicast, or unicast flood on a port?
A. port security
B. storm control
C. dynamic ARP inspection
D. BPDU guard
E. root guard
F. dot1x
Answer: B
QUESTION 116
You are a security engineer at a large multinational retailer. Your Chief Information Officer recently attended a security conference and has asked you to secure the network infrastructure from VLAN hopping.
Which statement describes how VLAN hopping can be avoided?
A. There is no such thing as VLAN hopping because VLANs are completely isolated.
B. VLAN hopping can be avoided by using IEEE 802.1X to dynamically assign the access VLAN to all endpoints and setting the default access VLAN to an unused VLAN ID.
C. VLAN hopping is avoided by configuring the native (untagged) VLAN on both sides of an ISL trunk to an unused VLAN ID.
D. VLAN hopping is avoided by configuring the native (untagged) VLAN on both sides of an IEEE 802.1Q trunk to an unused VLAN ID.
Answer: D
QUESTION 117
You are the administrator of a Cisco ASA 9.0 firewall and have been tasked with ensuring that the Firewall Admins Active Directory group has full access to the ASA configuration. The Firewall Operators Active Directory group should have a more limited level of access.
Which statement describes how to set these access levels?
A. Use Cisco Directory Agent to configure the Firewall Admins group to have privilege level 15 access. Also configure the Firewall Operators group to have privilege level 6 access.
B. Use TACACS+ for Authentication and Authorization into the Cisco ASA CLI, with ACS as the AAA server. Configure ACS CLI command authorization sets for the Firewall Operators group.
Configure level 15 access to be assigned to members of the Firewall Admins group.
C. Use RADIUS for Authentication and Authorization into the Cisco ASA CLI, with ACS as the AAA server. Configure ACS CLI command authorization sets for the Firewall Operators group.
Configure level 15 access to be assigned to members of the Firewall Admins group.
D. Active Directory Group membership cannot be used as a determining factor for accessing the Cisco ASA CLI.
Answer: B
QUESTION 118
A router is being enabled for SSH command line access.
The following steps have been taken:
– The vty ports have been configured with transport input SSH and login local.
– Local user accounts have been created.
– The enable password has been configured.
What additional step must be taken if users receive a ‘connection refused’ error when attempting to access the router via SSH?
A. A RSA keypair must be generated on the router
B. An access list permitting SSH inbound must be configured and applied to the vty ports
C. An access list permitting SSH outbound must be configured and applied to the vty ports
D. SSH v2.0 must be enabled on the router
Answer: A
QUESTION 119
Which two configurations are necessary to enable password-less SSH login to an IOS router? (Choose two.)
A. Enter a copy of the administrator’s public key within the SSH key-chain
B. Enter a copy of the administrator’s private key within the SSH key-chain
C. Generate a 512-bit RSA key to enable SSH on the router
D. Generate an RSA key of at least 768 bits to enable SSH on the router
E. Generate a 512-bit ECDSA key to enable SSH on the router
F. Generate a ECDSA key of at least 768 bits to enable SSH on the router
Answer: AD
QUESTION 120
Which two features does Cisco Security Manager provide? (Choose two.)
A. Configuration and policy deployment before device discovery
B. Health and performance monitoring
C. Event management and alerting
D. Command line menu for troubleshooting
E. Ticketing management and tracking
Answer: BC
Braindump2go Regular Updates of Cisco 300-206 Preparation Materials Exam Dumps, with Accurate Answers, Keeps the Members One Step Ahead in the Real 300-206 Exam. Field Experts with more than 10 Years Experience in Certification Field work with us.

http://www.braindump2go.com/300-206.html