[NEW QUESTIONS][FREE]Braindump2go 350-018 Exam Ref Download
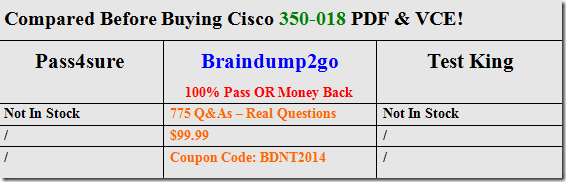
2016 FEBRUARY 350-018 Certification Exam NEW UPDATED: CCIE Security Written Exam, v4.0 is updated Today! 2016 Latest 350-018 PDF & 350-018 VCE can be free download from Braindump2go Now! 2016 NEW 350-018 Dumps and 350-018 Exam Questions Full Valid Version can be free downloaded now!
The Cisco CCIE® Security Written Exam (350-018) version 4.0 is a 2-hour test with 90–110 questions. This exam tests the skills and competencies of security professionals in terms of describing, implementing, deploying, configuring, maintaining, and troubleshooting Cisco network security solutions and products, as well as current industry best practices and internetworking fundamentals.
Topics include networking fundamentals and security-related concepts and best practices, as well as Cisco network security products and solutions in areas such as VPNs, intrusion prevention, firewalls, identity services, policy management, and device hardening. Content includes both IPv4 and IPv6 concepts and solutions.
350-018 Dump,350-018 PDF,350-018 VCE,350-018 Study Guide,350-018 Latest Dumps,350-018 Actual Test,350-018 Test Questions,350-018 Questions & Answers,350-018 Book,350-018 Braindump,350-018 CCIE Security Written Exam,350-018 Practice Tests
QUESTION 716
Refer to the exhibit. What is the effect of the given ACL Policy?

A. The policy will deny all ipv6 eBGP session
B. The policy will deny all ipv6 routed packets
C. The policy will disable ipv6 source routing
D. The policy will deny all ipv6 routing packet
Answer: C
QUESTION 717
What are three scanning engine that the Cisco IronPort dynamic vectoring and streaming engine can use to protect against malware? (Choose three)
A. McAfee
B. F-Secure
C. TrendMicro
D. Symantec
E. Webroot
F. Sophos
Answer: AEF
QUESTION 719
Which three statements about VRF aware Cisco Firewall are true? (Choose three)
A. It enables service providers to implement firewall on PE devices
B. It can run as more than one instance
C. It’s can support VPN network with overlapping address range without NAT
D. It can generate syslog message that are visible only to individual VPN
E. Its support both global and per-VRF commands and DOS parameter
F. It enables service
Answer: ABD
QUESTION 720
Which two statements about router advertisement message are true? (Choose two)
A. Message are sent to the multicast address FF02::1
B. Local link prefixes are shared automatically
C. Flag settings are shared in the message and retransmitted on the link
D. Router solicitation message are sent in response to Router Advertisement message
E. It support a configurable number of retransmission attempt for neighbor solicitation message
F. Each prefix included in the advertisement carrier’s lifetime information for that prefix
Answer: BC
QUESTION 721
What are three benefits of Cisco IOS FlexVPN? (Choose three)
A. Its provide hierarchical QoS on a per-tunnel basis
B. It is compatible with most private intranet deployments
C. Its support TACACS+
D. It is compatible with IKEv2-based third-party VPN solutions
E. It provides centralized policy control
F. It support DMVPN deployment
Answer: ADE
QUESTION 722
What is an example of a WEP cracking attack?
A. Reflected XSS attack
B. Dictionary travelers attack
C. SQL injection attack
Answer: B
QUESTION 723
From what type of server can you to transfer files to ASA’s internal memory
A. SSH
B. Netlogon
C. SFTP
D. SMB
Answer: D
QUESTION 724
What are three of the components of the Cisco PCI solution framework (choose three)
A. Infrastructure
B. Risk Assessment
C. Virtualization
D. Endpoint
E. Disaster management
F. Services
Answer: ADF
QUESTION 725
Which ASA device is designated as the cluster master?
A. the ASA with the highest MAC address
B. the ASA with the lowest MAC address
C. the ASA configured with the highest priority value
D. the ASA configures with lowest priority value
Answer: D
QUESTION 726
Refer the exhibit if R1 is acting as a DHCP server, what action can you take to enable the PC to receive an IP address assignment from the DHCP server?

A. Configure the ip helper-address command on R2 to use R1’s IP address
B. Configure the ip helper-address command on R1 to use R2’s ip address
C. Configure DHCP option 150 on R2
D. configure the ip local pool command on R2
E. Configure the ip loca pool command on R1
F. Configure DHCP option 82 on R1
Answer: A
QUESTION 727
What are the features of Cisco IOS that can help mitigate Blaster worm attack on RPC ports? (Choose two)
A. DCAR
B. dynamic ARP inspection
C. FPM
D. IP Source Guard
E. NABAR
F. URPF
Answer: CF
QUESTION 728
What port has IANA assigned to the GDOI protocol?
A. UDP 1812
B. UDP 500
C. UDP 848
D. UDP 4500
Answer: C
QUESTION 729
Which two statements about DHCP snooping are true? (Choose two)
A. The lease time in the banding database is a pre-set value
B. The binding database stores information about both IP and MAC addresses.
C. Message sent from outside the service-provider network is untrusted
D. The binding database stores information about trusted interface
E. DHCP servers connect to untrusted interface on the switch
Answer: AB
QUESTION 730
What is the maximum pattern length support by FPM search within a packet?
A. 128 bytes
B. 256 bytes
C. 512 bytes
D. 1500 bytes
Answer: B
QUESTION 731
What are three IPv6 extension headers? (Choose three)
A. Authentication
B. Destination options
C. Source options
D. Hop-by-hop options
E. TTL
F. Segment
Answer: ABD
QUESTION 732
Which statement about the Cisco AnyConnect web Security module is true?
A. It is VPN client software that works over the SSL protocol
B. It is deployment on endpoints to route HTTP traffic to ScanSafe
C. It is an endpoint component that is used with smart tunnels in a clientless SSL VPN
D. It operates as an NAC Agent when it is configured with AnyConnect VPN client
Answer: B
The following topics are general guidelines for the content likely to be included on the exam.
1. Infrastructure, Connectivity, Communications, and Network Security 20%
2. Security Protocols 15%
3. Application and Infrastructure Security 10%
4. Threats, Vulnerability Analysis, and Mitigation 10%
5. Cisco Security Products, Features, and Management 20%
6. Cisco Security Technologies and Solutions 17%
7. Security Policies and Procedures, Best Practices, and Standards 8%
2016 NEW 350-018 Study Guide PDF & 350-018 Dumps PDF Help you 100% Pass 350-018 CCIE Certification Exam! http://www.braindump2go.com/350-018.html (775q)